Flask Request.remote_Addr Exploit . Sys.exit() it works fine, but i just would like to ask how reliable and safe this. Getting `127.0.0.1` as a client's ip address is easy: For example a combination of range and etag in a head request can leak the content of the page via head requests: We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. A request with the header. Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: Write your own message, and get flag! The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). Today, let’s discuss one of them, a vulnerability found in flask applications that can lead to remote code execution (rce). It is my first flask project with nginx.
from blog.csdn.net
It is my first flask project with nginx. The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. Write your own message, and get flag! Getting `127.0.0.1` as a client's ip address is easy: Today, let’s discuss one of them, a vulnerability found in flask applications that can lead to remote code execution (rce). A request with the header. For example a combination of range and etag in a head request can leak the content of the page via head requests: Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: Sys.exit() it works fine, but i just would like to ask how reliable and safe this.
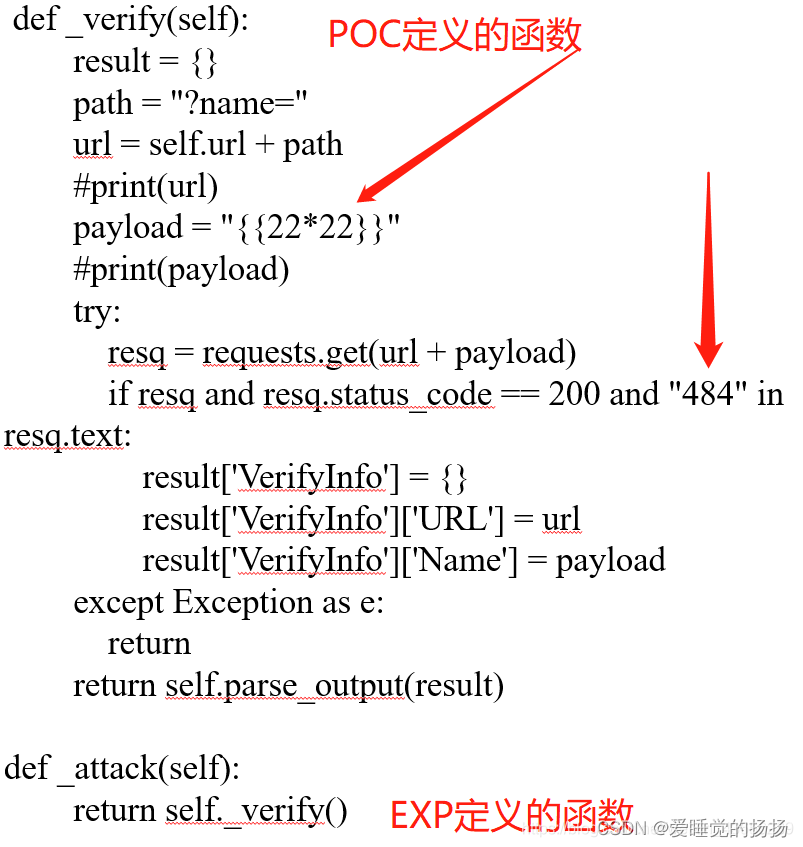
pocsuite3安装及使用CSDN博客
Flask Request.remote_Addr Exploit The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). Write your own message, and get flag! A request with the header. Sys.exit() it works fine, but i just would like to ask how reliable and safe this. For example a combination of range and etag in a head request can leak the content of the page via head requests: Today, let’s discuss one of them, a vulnerability found in flask applications that can lead to remote code execution (rce). Getting `127.0.0.1` as a client's ip address is easy: It is my first flask project with nginx. Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips:
From qiita.com
【Flask】request.args実行時のエラー違いを確認する Python Qiita Flask Request.remote_Addr Exploit Today, let’s discuss one of them, a vulnerability found in flask applications that can lead to remote code execution (rce). The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). Write your own message, and get flag! It is my first flask project with nginx. Getting `127.0.0.1` as a client's ip address. Flask Request.remote_Addr Exploit.
From cloud.tencent.com
Python Flask 编程 连载 03 Flask 请求腾讯云开发者社区腾讯云 Flask Request.remote_Addr Exploit The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). It is my first flask project with nginx. Today, let’s discuss one of them, a vulnerability found in flask applications that can lead to remote code execution (rce). Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: Write your own message, and get flag!. Flask Request.remote_Addr Exploit.
From github.com
GitHub blue0x1/mobilemouseexploit Mobile Mouse 3.6.0.4 could allow Flask Request.remote_Addr Exploit Getting `127.0.0.1` as a client's ip address is easy: The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). Sys.exit() it works fine, but i just would like to ask how reliable and safe this. For example a combination of range and etag in a head request can leak the content of. Flask Request.remote_Addr Exploit.
From www.codingthesmartway.com
Generating a Flask REST API with ChatGPT A StepbyStep Guide Flask Request.remote_Addr Exploit Getting `127.0.0.1` as a client's ip address is easy: For example a combination of range and etag in a head request can leak the content of the page via head requests: We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. A request with the header. Today, let’s discuss one of them, a vulnerability found. Flask Request.remote_Addr Exploit.
From www.geeksforgeeks.org
Get the Data Received in a Flask request Flask Request.remote_Addr Exploit A request with the header. For example a combination of range and etag in a head request can leak the content of the page via head requests: It is my first flask project with nginx. We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. Today, let’s discuss one of them, a vulnerability found in. Flask Request.remote_Addr Exploit.
From slideplayer.com
Chapter 2 Application layer ppt download Flask Request.remote_Addr Exploit We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. Sys.exit() it works fine, but i just would like to ask how reliable and safe this. The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). Today, let’s discuss one of them, a vulnerability found in flask. Flask Request.remote_Addr Exploit.
From ithelp.ithome.com.tw
Day23 flask request JSON iT 邦幫忙一起幫忙解決難題,拯救 IT 人的一天 Flask Request.remote_Addr Exploit It is my first flask project with nginx. A request with the header. Today, let’s discuss one of them, a vulnerability found in flask applications that can lead to remote code execution (rce). Sys.exit() it works fine, but i just would like to ask how reliable and safe this. For example a combination of range and etag in a head. Flask Request.remote_Addr Exploit.
From www.youtube.com
Flask Request Object YouTube Flask Request.remote_Addr Exploit Getting `127.0.0.1` as a client's ip address is easy: The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). It is my first flask project with nginx. Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: For example a combination of range and etag in a head request can leak the content of the. Flask Request.remote_Addr Exploit.
From www.delftstack.com
Handle Request Data in JSON Format in Flask Delft Stack Flask Request.remote_Addr Exploit The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). Write your own message, and get flag! We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. It is my first flask project with nginx. Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: Sys.exit() it works fine, but. Flask Request.remote_Addr Exploit.
From opheliakemble1993.blogspot.com
Ophelia Kemble Flask Run On Ip And Port Flask Request.remote_Addr Exploit Getting `127.0.0.1` as a client's ip address is easy: A request with the header. Write your own message, and get flag! It is my first flask project with nginx. Sys.exit() it works fine, but i just would like to ask how reliable and safe this. We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and.. Flask Request.remote_Addr Exploit.
From blog.csdn.net
pocsuite3安装及使用CSDN博客 Flask Request.remote_Addr Exploit Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. Sys.exit() it works fine, but i just would like to ask how reliable and safe this. For example a combination. Flask Request.remote_Addr Exploit.
From slideplayer.com
Program Analysis for Security ppt download Flask Request.remote_Addr Exploit It is my first flask project with nginx. Write your own message, and get flag! For example a combination of range and etag in a head request can leak the content of the page via head requests: Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: Getting `127.0.0.1` as a client's ip address is easy: Sys.exit() it works fine, but i just. Flask Request.remote_Addr Exploit.
From www.nurmatova.com
Flask based Web Applications Flask Request.remote_Addr Exploit Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: For example a combination of range and etag in a head request can leak the content of the page via head requests: The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). It is my first flask project with nginx. Today, let’s discuss one of. Flask Request.remote_Addr Exploit.
From testdriven.io
Developing Web Applications with Python and Flask Routing TestDriven.io Flask Request.remote_Addr Exploit It is my first flask project with nginx. A request with the header. Sys.exit() it works fine, but i just would like to ask how reliable and safe this. We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. Today, let’s discuss one of them, a vulnerability found in flask applications that can lead to. Flask Request.remote_Addr Exploit.
From github.com
GitHub Narasimha1997/py4jshell Simulating Log4j Remote Code Flask Request.remote_Addr Exploit The exploit is performed with a get request like the following (or using 0.0.0.0 for the ip address). Sys.exit() it works fine, but i just would like to ask how reliable and safe this. We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: Getting `127.0.0.1` as a. Flask Request.remote_Addr Exploit.
From portswigger.net
Exploit drops for remote code execution bug in Control Web Panel The Flask Request.remote_Addr Exploit Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: It is my first flask project with nginx. Write your own message, and get flag! We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. Sys.exit() it works fine, but i just would like to ask how reliable and safe this. For example a combination of range and. Flask Request.remote_Addr Exploit.
From testdriven.io
Deep Dive into Flask's Application and Request Contexts TestDriven.io Flask Request.remote_Addr Exploit For example a combination of range and etag in a head request can leak the content of the page via head requests: Getting `127.0.0.1` as a client's ip address is easy: A request with the header. It is my first flask project with nginx. We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. The. Flask Request.remote_Addr Exploit.
From platzi.com
Implementación de FlaskBootstrap y FlaskWTF Platzi Flask Request.remote_Addr Exploit We access the remote address directly with request.remote_addr, through the remote_addr key from request.environ, and. Good_ips = ['127.0.0.1','192.168.1.10','192.168.1.1'] if request.remote_addr in good_ips: Today, let’s discuss one of them, a vulnerability found in flask applications that can lead to remote code execution (rce). Sys.exit() it works fine, but i just would like to ask how reliable and safe this. A request. Flask Request.remote_Addr Exploit.